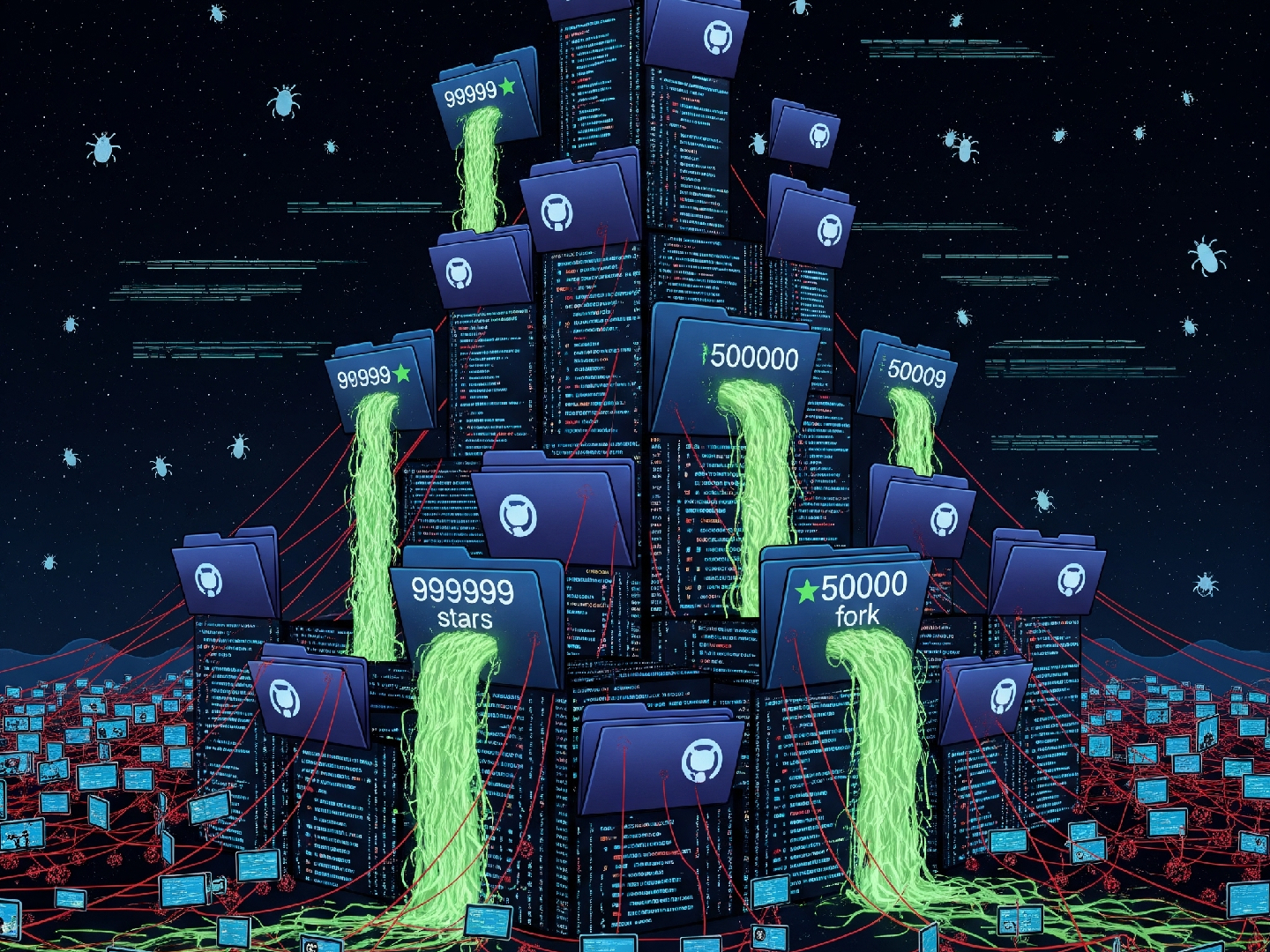
CastleLoader Malware Spreads Through Bogus GitHub Repos, Hits Hundreds
A sophisticated new malware loader dubbed CastleLoader is making waves in the cybersecurity world. Researchers have...
Read More