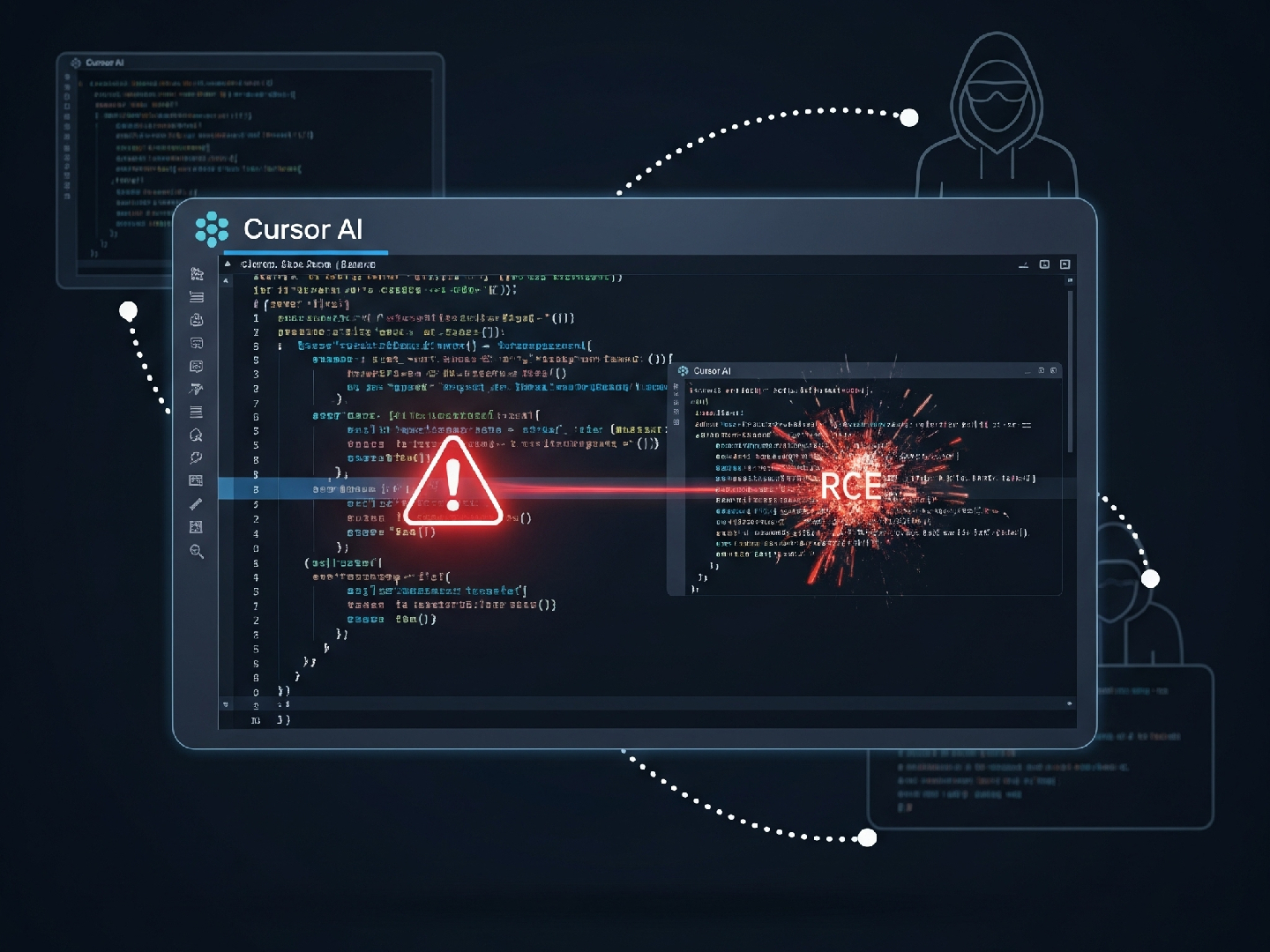
Deleted VS Code Extensions Can Be Resurrected by Attackers, Experts Warn
A security vulnerability in the Visual Studio Code Marketplace could allow malicious actors to hijack the names of...
Read More